![PDF] Efficient Technical and Organizational Measures for Privacy-aware Campus Identity Management and Service Integration | Semantic Scholar PDF] Efficient Technical and Organizational Measures for Privacy-aware Campus Identity Management and Service Integration | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5ae06e435a9ef0d4b315a24a0ff29f953982531e/4-Figure2-1.png)
PDF] Efficient Technical and Organizational Measures for Privacy-aware Campus Identity Management and Service Integration | Semantic Scholar

A Failure to "Do No Harm" -- India's Aadhaar biometric ID program and its inability to protect privacy in relation to measures in Europe and the U.S. - Abstract - Europe PMC
TECHNICAL AND ORGINIZATIONAL MEASURES (FOR SUPPLIERS) These Technical and Organizational Measures (the “TOMs”) are an integ

White Paper. How Secure is FastViewer? Results of a Security Analysis by the Fraunhofer AISEC and. Fraunhofer ESK Institutes - PDF Free Download
![PDF] Information Systems Security Measures and Countermeasures: Protecting Organizational Assets from Malicious Attacks | Semantic Scholar PDF] Information Systems Security Measures and Countermeasures: Protecting Organizational Assets from Malicious Attacks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/fc05a260160533919c1240a0de00873ba0144e8d/5-Table2-1.png)
PDF] Information Systems Security Measures and Countermeasures: Protecting Organizational Assets from Malicious Attacks | Semantic Scholar
PLOS ONE: Measuring Information Security Performance with 10 by 10 Model for Holistic State Evaluation
Data protection statement The protection of your privacy in processing personal data as well as the security of all business dat
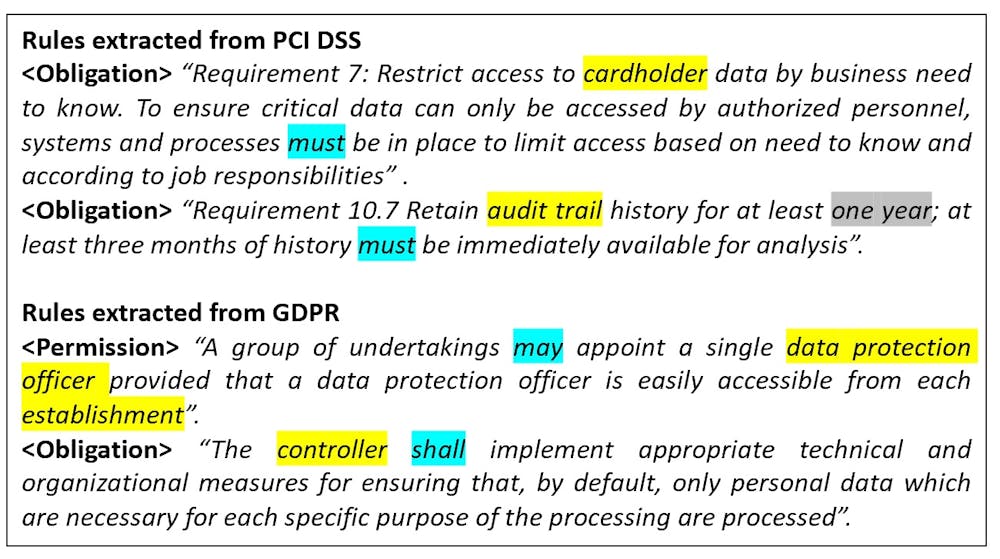
AI could constantly scan the internet for data privacy violations, a quicker, easier way to enforce compliance

Handbook for practical implementation of the Regulation for the technical and organizational measures to ensure confidentiality and protection of personal data | Агенција за заштита на личните податоци
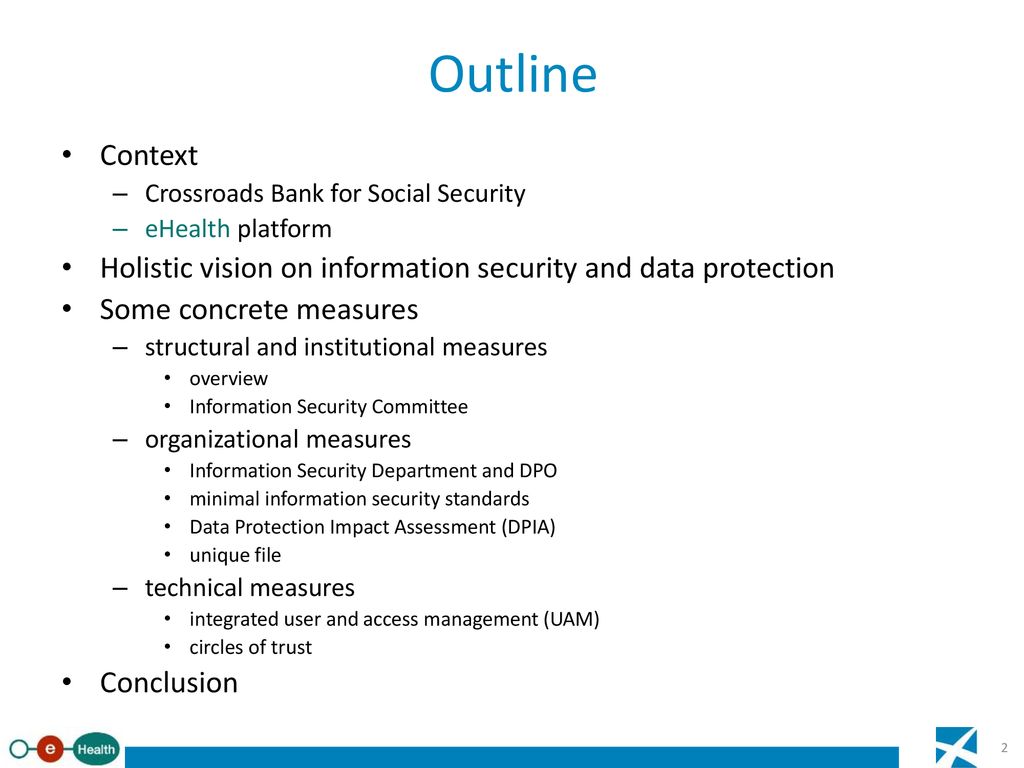
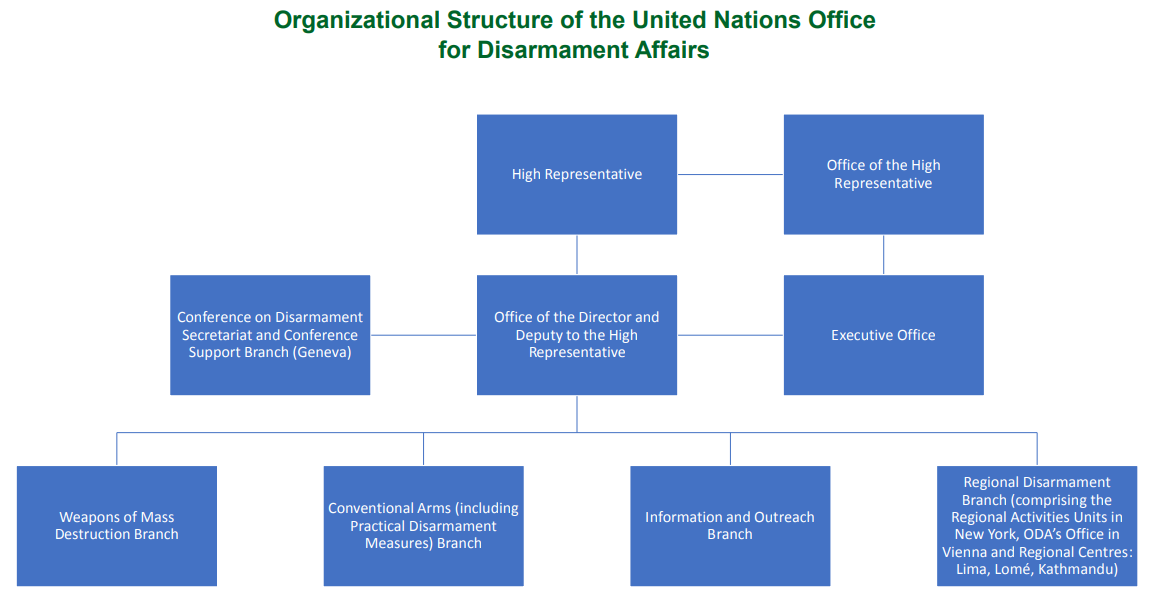
A practice testimony on the implementation of information security and data protection at the Crossroads Bank for Social Security and the eHealth platform. - ppt download
iNEXT-Discovery Privacy Policy Anyone whose personal data is processed has the right to file a complaint with the competent auth
Privacy statement Entecom Systems NV processes personal information in compliance with this privacy statement. For further infor

Organizational Structure Leadership Initiatives Programs Investment Measures Scorecards | PowerPoint Presentation Slides | PPT Slides Graphics | Sample PPT Files | Template Slide